Two weeks ago we switched our Internet and copper phone-line to the NBN grid. (you have no choice 18 months after your street is hooked up)
Our Exetel ISP send out a free ZTE modern on their 12 month contacts. (while oddly selling NetComm modems for $80+)
Turns out the ZTE modem they send out has an enter antime they like ‘service’ back-door called TR-069 (see the above video showing how it’s hacked) which uses port 7547.
I did a port scan on the new ZTE … holy gecko poop, an open port!!
https://www.grc.com/x/portprobe=7547
Frantic me posted on the Exetel forum asking how to turn TR-069 off – but they were no help.
- Plan B, buy a better brand? Nah, just wasted booze money.
- Plan C, I like the challenge using what’s at hand, so I cascaded our old ADSL router >> ZTE LAN to WAN on the ADSL router.
LAN to WAN >> All the ZTE can see is one LAN in use, even with a dozen devices connected behind the ADSL router.
That got boring last night – one power board with too many bloody things plugged in … port test still failing and the ‘through speed’ seemed slower … so I ditched the ADSL router and did the following with success …
- Make sure you have your Exetel VDSL password handy. (note: VoIP password is different)
- Back up the default Exetel ZTE modem settings to a safe place.
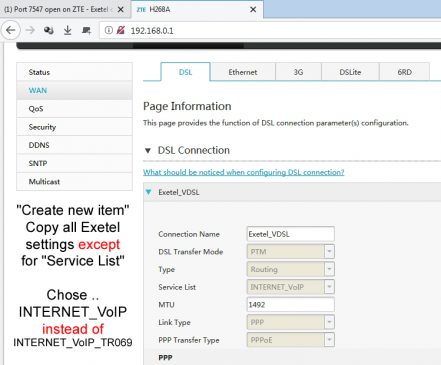
- WAN Settings >> WAN >> DSL Connection >> open Exetel_VDSL and note the factory settings.
- Then below it click “Create New Item”
- Copy everything in the Exetel_VDSL except for “Service List”
- In the new item select INTERNET_VoIP (or INTERNET only if you don’t have VoIP)
- Make sure your user name and password are correct.
- BEFORE clicking “APPLY”, delete the original Exetel_VDSL version. It will clear without refreshing the page.
- Our ZTE still had the obsolete “Exetel_ADSL” settings which was deleted too. (only delete it when you’re 100% on the NBN)
- Now click APPLY on the new Exetel_VDSL copy.
- Reboot the router and make sure you still have internet access.
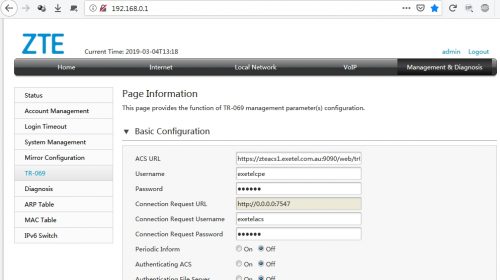
- Management and Diagnoses >> TR-069 >> switch all radio buttons to ‘off’.
- Head over to https://www.grc.com/x/portprobe=7547 and check that the port is now stealth.
NOTE: using fake info on the TR-069 page does NOT close the port.
It would have been nice to just have an on-off radio button in the TR-069 settings.
There must be a reason why Exetel sells better Netcomm’s. Being ZTE, and free, I still don’t trust these chicom things.





I had to hack my Telstra Gateway Frontier modem / router to disable the same thing. Its labelled CWMP in that router. How to hack it etc are at https://whirlpool.net.au/wiki/hack_technicolor
I suspect most if not all new modem / routers especially those provided by ISPs have a similar port open for remote management.
G’day Raff,
I bought an unlocked TP-Link VR400 VDSL off Bumtree three weeks ago ($5) and it didn’t have a simple TR on-off button either … or VoIP … so I flipped it for $50 a few days after … $5 of that went towards a Bumtree Telstra C6300BD-1TLAUS. (the handy 3a-12v psu was worth the drive)
Reading Whirlpool, turned out it has two admin areas as well. One for the dummies and one for Telstra. I didn’t notice any CWMP while in the hidden admin (I’ve since turfed the cable router) … but that’s the point .. all this hidden stuff going on.
I’ve never had a router OpenWRT would work on – but sounds like fun 🙂
How bloody hard is it for those like ZTE to have a simple TR-069 on/off switch. If ZTE is so secure, then I have to wonder why my ISP is / was selling Netcomms too. ZTE even disable the USB media port on these free versions. Bloody chicoms.
I hope you and the family are doing well.
Cheers,
Rodney 🙂